KEY FIGURES
More throughput, more power, more speed! 5G is heralded as the revolution that should improve the digital world for businesses and consumers alike.
While 5G will bring many technological advances, the risks associated with this "revolution" are still under-represented.
5G will transform the Internet into a gigantic corporate network and increase the flow of shared data; consequently, the use of the public cloud, which is unsecured and subject to extraterritoriality laws, will grow in the same proportions. Sensitive data will be much more exposed than with 4G, and is already becoming the object of an invisible war in the digital world. Corporate and national sovereignty will be severely tested.
Public liberties, national sovereignty and legal issues at stake
Tomorrow's wealth lies in our data, but we are still far too naïve: we entrust our confidential and personal data to non-European companies (US and China) without measuring the impact in terms of sovereignty (as in the case of the Health Data Hub entrusted to Microsoft). Under pressure from powerful lobbies, the digital system is gradually stripping politicians of their general policing powers in favor of administrative and technical policing, which is increasingly framing the powers of the state.
"With the massive arrival of 5G and the Public Cloud, the internet is becoming a giant enterprise network.
The data circulates in the clear and is accessible and manipulable by all: governments, hackers and competitors...
The Internet is becoming a pirate's playground. 5G technology enables direct intercommunication between computer terminals and connected objects: confidentiality and integrity become the new challenges for data sharing. The corollary is that if data remains unencrypted on networks, the Internet of the future opens the way to an Orwellian nightmare:
- At one end of the spectrum, the digital giants of liberal societies will track our digital uses down to the intimate with commercial motives while their intelligence agencies will file citizens by tracking their every action without limit;
- At the other end of the spectrum, dictatorships will control individual behavior by assigning social bonuses or penalties to each everyday action tracked by facial recognition, GPS, audio and webcam.
In any case, the right to privacy will gradually disappear and be replaced by a generation of manipulated or controlled digital slaves.
In the spirit of applying the European General Data Protection Regulation (GDPR), the only legal option likely to remain is to criminalize the exploitation of personal data and its exfiltration outside European territory, i.e. outside a virtual zone controlled by states, or better still by users themselves.
But national and a fortiori European digital sovereignty remains a myth today, even if the RGPD is a world first in terms of regulation. However, the European Court of Justice's "Schrems 2" ruling on July 16, 2020 invalidated the international "Privacy Shield" agreement allowing the transfer of European citizens' data to the USA, thus sending out a strong signal of a desire for European sovereignty.
Technical and digital challenges
"More connections = greater risk of cyberattack".
The very high connection density offered by 5G is not without consequences: the greater the number of terminals connected in the same space, the greater the potential for security breaches. This exposes companies' IT systems and multiplies the risk of cyber-attacks. With 5G, CISOs will have to provide even more resources to secure their systems than with 4G.
Energy and health issues
5G is incompatible with 4G. Its deployment will require the replacement of all existing antennas and terminals. While it is more economical in terms of power consumption, by around 40%, it will lead to an explosion in uses, particularly video. The consensus is that power consumption by mobile operators will increase threefold over the next five years.
Moreover, while thousands of studies tend to show that waves have a biological impact on health by acting in particular on the blood-brain barrier, the WHO declared in 2018: " To date, no harmful health effects caused by the use of a cell phone have been demonstrated ."
We still know nothing about the impact of millimeter waves on insects, particularly whether or not there is a vital interaction with their antennae, which connect them to their environment, as is suspected.
Should we give up on 5G?
Of course, 5G will enable breakthroughs in various technical and scientific fields. So it's not a question of giving up on it, but of thinking carefully about the uses and risks to make sure we really need it, because all progress comes at a price.
European laws protect sensitive personal data, while at the same time extraterritorial laws threaten state sovereignty. Faced with intelligence agencies that have industrialized industrial and political espionage, legal protection alone is not enough.
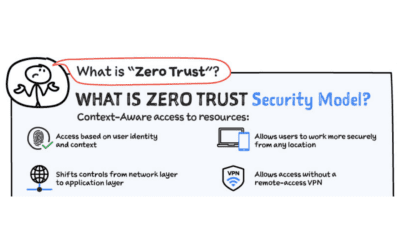
The only solution to truly secure data is the "ZERO TRUST" concept, but which trusted third parties should we be working with? The GAFAMs are the key players in the Public Cloud, and they are candidates for the role of trusted third parties for the "ZERO TRUST", but can we trust them in the context of the legal threat of extraterritoriality laws to which they are subject?
The only technical option for preserving our privacy is to give control of the data back to the end-user, by decentralizing security to the user terminal, and consequently for governments to eventually regain control over the hardware and software that control our terminals, by making hardware that is both generic and government-approved mandatory.

Thierry Leblond
Co-founder & CEO Scille SCILLE