Dive into the innovation
in security
With the best of technology combined with the best of security


Make intrusion totally impossible
With our unique end-to-end data encryption technology, you'll make intrusion impossible, both during transmission and storage. The sensitive file is not only locked with keys that are only available to authorized users, but it is also sliced so that each piece of data is encrypted. Thus, if a malicious software intercepts the confidential document, it will only discover a perfectly unreadable fragment.
Get your mathematical proof authenticated
Our Zero Knowledge innovation authenticates authorized users, without requiring their identity to prevent it from being disclosed. The certification is done by an entity, called a "proof provider", which mathematically proves to another entity, the "verifier", that a proposition is true without revealing any information other than the truth of the proposition itself.
Discover the PARSEC technology in video
Protect your sensitive data with security innovation
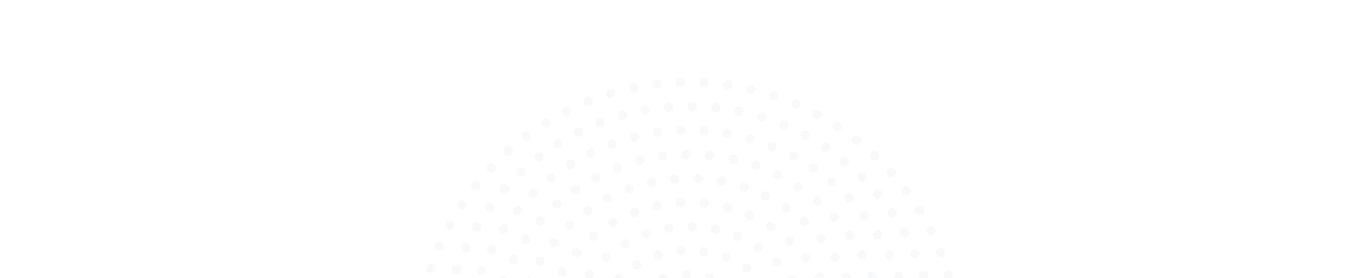
Certification of your workstation
considered as the only trusted entity
Splitting your files into several blocks
stored on different public or private clouds
End-to-end encryption of each chopped block
to block the privileges of unauthorized users

"Anticipating future needs and integrating security by design, while remaining very easy to use, PARSEC has a software architecture based on concepts and algorithms from Research, which guarantees :
- Privacy
- Integrity
- Resilience
- Availability "
"Developed by Scille in collaboration with the Laboratoire Bordelais de Recherche en Informatique, PARSEC is a state-of-the-art solution.
Thierry Leblond, CEO & Co-founder of PARSEC

Advice from our cyber security experts
Intel Software Guard Extensions
INTRO In a context of health crisis, companies are increasingly required to work with remote employees. In order to protect themselves from cyber attacks and to protect their critical data, various solutions are possible. At Parsec, we...
Our experience with Hypothesis testing (and why do we love it so much!)
Intro At Scille, we are developing Parsec : an open-source zero-trust file sharing software (think of it as a Dropbox with full client-side encryption). The project has been in development for 4 years (5k commits on master, 12 contributors) and has been used...